Navigating the cloud landscape requires vigilance, and that starts with understanding the posture of your cloud security. A cloud security audit is more than just a compliance checkbox; it’s a vital process that ensures your data, applications, and infrastructure are protected from evolving threats. This comprehensive guide will explore the key aspects of cloud security audits, helping you understand their importance, scope, and how to conduct them effectively.
Understanding Cloud Security Audits
What is a Cloud Security Audit?
A cloud security audit is a systematic evaluation of your organization’s cloud environment to assess its security posture. It involves examining the policies, procedures, controls, and technologies implemented to protect data and infrastructure in the cloud. The audit aims to identify vulnerabilities, risks, and areas for improvement, ensuring compliance with relevant regulations and industry best practices.
Why are Cloud Security Audits Important?
Performing regular cloud security audits offers several critical benefits:
- Risk Mitigation: Identifies and addresses vulnerabilities before they can be exploited by attackers.
- Compliance: Ensures adherence to industry regulations like GDPR, HIPAA, PCI DSS, and SOC 2.
- Cost Optimization: Pinpoints inefficient security practices that lead to unnecessary expenses.
- Improved Security Posture: Enhances overall security by implementing robust controls and policies.
- Data Protection: Safeguards sensitive data from unauthorized access, loss, or theft.
- Customer Trust: Builds trust with customers by demonstrating a commitment to security.
Who Needs a Cloud Security Audit?
Any organization that stores or processes data in the cloud should conduct regular cloud security audits. This includes businesses of all sizes and across various industries, such as:
- Financial institutions
- Healthcare providers
- E-commerce companies
- Software developers
- Government agencies
Example: A healthcare provider storing patient data on AWS must conduct regular HIPAA compliance audits to ensure the confidentiality and integrity of electronic Protected Health Information (ePHI).
The Cloud Security Audit Process
Planning and Preparation
The success of a cloud security audit hinges on careful planning. This phase involves defining the scope, objectives, and methodology of the audit. Key steps include:
- Defining the Scope: Determine the specific cloud services, applications, and data to be included in the audit.
- Identifying Objectives: Establish clear goals, such as achieving compliance, reducing risks, or improving security posture.
- Selecting an Audit Team: Assemble a team of experienced security professionals with expertise in cloud technologies. This could be an internal team, external consultants, or a hybrid approach.
- Defining Methodology: Choose a suitable audit framework, such as the Cloud Security Alliance (CSA) Cloud Controls Matrix (CCM) or the NIST Cybersecurity Framework.
Example: An e-commerce company might define the scope of its audit to include its AWS S3 buckets storing customer data, its EC2 instances running its website, and its RDS database containing order information. The objective could be to ensure PCI DSS compliance.
Data Collection and Analysis
This phase involves gathering relevant data from the cloud environment and analyzing it to identify vulnerabilities and risks. This may include:
- Configuration Reviews: Assessing the configuration settings of cloud services, such as IAM roles, security groups, and storage policies.
- Vulnerability Scanning: Performing automated scans to identify known vulnerabilities in cloud instances and applications. Tools such as Nessus, Qualys, and Rapid7 are commonly used.
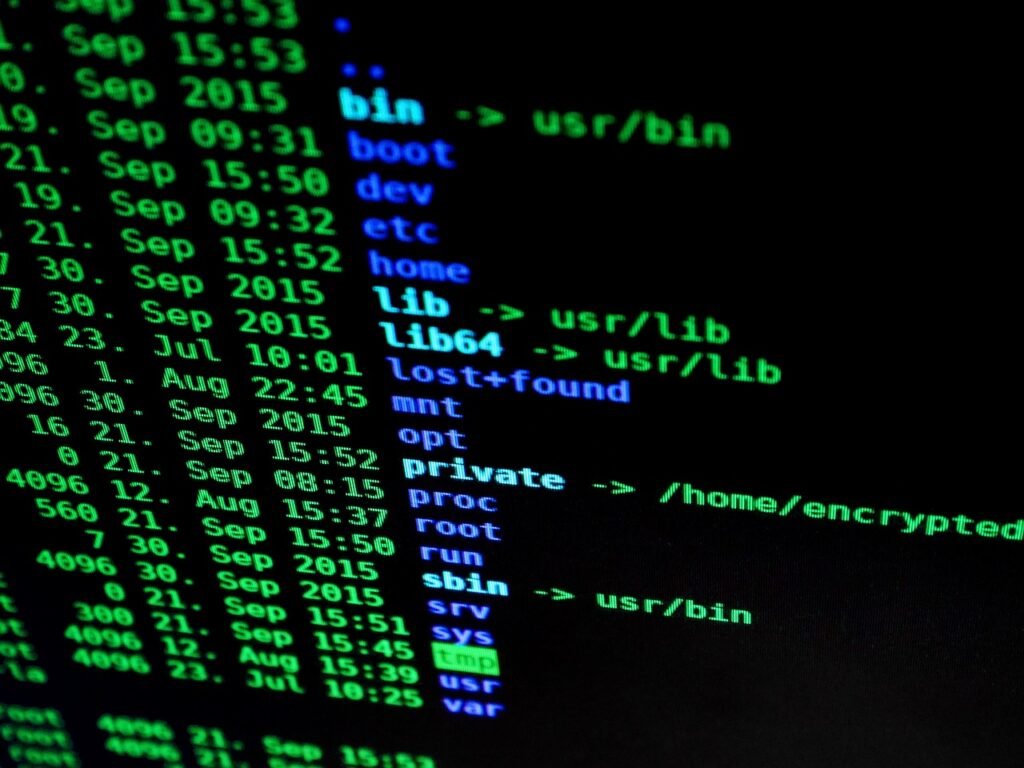
- Log Analysis: Examining cloud logs to detect suspicious activities, security incidents, and policy violations. CloudTrail (AWS), Azure Monitor, and Google Cloud Logging are key resources.
- Penetration Testing: Simulating real-world attacks to identify weaknesses in the cloud environment.
- Policy and Procedure Reviews: Evaluating the effectiveness of security policies and procedures, such as incident response plans and data backup strategies.
Example: Analyzing CloudTrail logs reveals that an IAM user with limited permissions attempted to access an S3 bucket containing sensitive financial data. This indicates a potential insider threat or compromised account.
Reporting and Remediation
After the data collection and analysis phase, the audit team prepares a detailed report outlining the findings, recommendations, and prioritized action items. This report should include:
- Executive Summary: A high-level overview of the audit findings and recommendations.
- Detailed Findings: A description of each vulnerability, risk, and non-compliance issue identified during the audit.
- Risk Assessment: An evaluation of the potential impact and likelihood of each risk.
- Recommendations: Specific steps to remediate the identified vulnerabilities and risks.
- Prioritization: A ranking of the recommendations based on their severity and impact.
The remediation phase involves implementing the recommendations outlined in the audit report. This may involve:
- Patching Vulnerabilities: Applying security updates to cloud instances and applications.
- Strengthening Configurations: Tightening security configurations of cloud services.
- Improving Policies and Procedures: Updating security policies and procedures to address identified gaps.
- Implementing Security Controls: Deploying new security controls, such as intrusion detection systems and data loss prevention (DLP) solutions.
Example: The audit report recommends enabling multi-factor authentication (MFA) for all IAM users to prevent unauthorized access. The remediation step involves implementing MFA for all user accounts and enforcing its use through IAM policies.
Key Considerations for Cloud Security Audits
Compliance Requirements
Cloud security audits are often driven by compliance requirements. Depending on the industry and location, organizations may need to comply with regulations such as:
- GDPR: General Data Protection Regulation (Europe)
- HIPAA: Health Insurance Portability and Accountability Act (US)
- PCI DSS: Payment Card Industry Data Security Standard
- SOC 2: Service Organization Control 2
- ISO 27001: International Organization for Standardization 27001
Example: A financial institution storing customer data in the cloud must comply with regulations such as GLBA (Gramm-Leach-Bliley Act) and PCI DSS, which require regular security assessments and penetration testing.
Cloud-Specific Challenges
Auditing cloud environments presents unique challenges compared to traditional on-premises systems:
- Shared Responsibility Model: Understanding the division of security responsibilities between the cloud provider and the customer.
- Dynamic Environments: Managing the constantly changing nature of cloud infrastructure.
- Complex Configurations: Dealing with the intricate configurations of cloud services.
- Lack of Visibility: Overcoming limitations in visibility into the cloud environment.
Example: Under the AWS shared responsibility model, AWS is responsible for the security of the cloud (e.g., physical security of data centers), while the customer is responsible for the security in the cloud (e.g., configuring security groups, managing IAM roles, patching operating systems).
Automation and Tools
Leveraging automation and security tools can streamline the cloud security audit process and improve its effectiveness. Consider using tools for:
- Configuration Management: Automating the configuration and monitoring of cloud resources. (e.g., AWS Config, Azure Policy)
- Vulnerability Scanning: Identifying vulnerabilities in cloud instances and applications. (e.g., Nessus, Qualys Cloud Platform)
- Security Information and Event Management (SIEM): Collecting and analyzing security logs from various sources. (e.g., Splunk, Sumo Logic, Azure Sentinel)
- Cloud Security Posture Management (CSPM): Continuously monitoring and assessing the security posture of the cloud environment. (e.g., Dome9, CloudCheckr, Palo Alto Prisma Cloud)
Best Practices for Cloud Security Audits
Continuous Monitoring
Instead of conducting audits as isolated events, implement continuous monitoring to proactively identify and address security issues. Utilize tools like CloudWatch (AWS) or Azure Monitor for real-time insights.
Regular Audits
Establish a schedule for regular cloud security audits based on the organization’s risk profile and compliance requirements. Quarterly or annual audits are common.
Strong Authentication and Access Control
Implement robust authentication and access control mechanisms, such as multi-factor authentication (MFA) and the principle of least privilege. Regularly review and update IAM policies.
Data Encryption
Encrypt sensitive data both in transit and at rest. Use encryption keys managed by a key management service (KMS) to protect data from unauthorized access.
Incident Response Plan
Develop and regularly test an incident response plan to effectively respond to security incidents in the cloud environment. Include procedures for identifying, containing, eradicating, and recovering from incidents.
Conclusion
A well-executed cloud security audit is an indispensable part of maintaining a robust security posture in the cloud. By understanding the process, challenges, and best practices, organizations can effectively protect their data, ensure compliance, and build customer trust. Embrace continuous monitoring, automation, and a proactive approach to cloud security to stay ahead of evolving threats and maximize the benefits of cloud computing. Remember that a cloud security audit is not a one-time event, but rather an ongoing process of continuous improvement and vigilance.







